New Windows Exploits: 12 Urgent Steps Small Firms and Solo Law Practices Must Take Now
For small businesses and solo or boutique law firms, Windows endpoints are the backbone of client work—briefs, billing, eDiscovery, and confidential strategy memos all live there. When new Windows security exploits emerge, attackers don’t wait for you to catch up; they automate and aim straight at firms with lean IT. This week is the right week to close the gaps. Below is a focused, business-first action plan you can execute in days, not months, to harden Windows, reduce attack surface, and keep client data safe—without derailing billable work or breaking your budget.
- A quick threat briefing: why Windows exploits hit small firms hardest
- The first 24 hours: contain, patch, verify
- Within 72 hours: harden identity and endpoints
- Your 7‑day sprint: shrink attack surface and persistence paths
- Which controls do what? Quick comparison table
- Backups, recovery, and a 90‑minute incident drill
- Build your small‑firm Windows security playbook
- Budget‑smart priorities for boutiques and solos
- Conclusion: move fast, then standardize
A quick threat briefing: why Windows exploits hit small firms hardest
Modern exploits rarely look like Hollywood hacks. They’re chains of small gaps—an unpatched privilege escalation here, a malicious document there, a weak MFA factor on a partner’s laptop. Attackers scan the internet for new opportunities within hours of disclosures and then pivot laterally through Remote Desktop, file shares, email, and SaaS apps. Small legal practices are especially attractive: they hold valuable information, are bound by strict confidentiality, and often have flat networks with shared admin passwords and inconsistent patching.
Think in three layers: (1) identity (accounts, MFA, Conditional Access), (2) endpoint (patches, EDR, device control), and (3) recovery (immutable backups, tested restores). If you strengthen all three, you turn “a single click” into a dead end.

The first 24 hours: contain, patch, verify
In the first day after credible exploit chatter or a security bulletin, your goal is to reduce exposure quickly and calmly. Use this checklist to move with confidence:
1) Freeze nonessential changes and confirm visibility
- Designate one decision-maker (often the managing partner or operations manager) and one technical lead (internal IT or a trusted MSP).
- Ensure you can see all Windows devices: firm-issued laptops/desktops, remote contractor machines that access files, and any Windows servers or NAS devices. Create a single spreadsheet or dashboard with hostname, user, OS version, and patch status.
2) Patch the right way: staged, fast, verified
- Enable automatic updates on all Windows 10/11 devices and set “Get the latest updates as soon as they’re available.” For centrally managed devices, push updates via your RMM, Intune/Windows Update for Business, or WSUS.
- Use ring-based deployment: pilot (IT/ops lead), then 20–30% of users with similar apps, then the remainder. Target high-risk roles first (partners, finance, anyone with admin rights).
- Reboot to complete updates; many kernel and SmartScreen fixes don’t take effect until after a restart. Verify build numbers and patch levels post-reboot.
3) Temporarily raise defenses
- Turn on tamper protection and cloud-delivered protection in Microsoft Defender (or your EDR). Enable real-time protection and require signatures to be current.
- If there is active exploit code in the wild, consider disabling macros for all but approved signers, blocking Office from launching child processes, and restricting script interpreters temporarily.
4) Look for quick indicators of trouble
- Alert on suspicious events: repeated failed logons (4625), creation of new local admins (4732), unexpected services installed (7045), cleared logs (1102), or new scheduled tasks (4698).
- Scan endpoints for credential theft attempts (e.g., LSASS access) and quarantine anything suspicious immediately.

Within 72 hours: harden identity and endpoints
Most real-world breaches begin with identity. By day three, treat account protection as nonnegotiable.
5) Enforce phishing-resistant MFA for all
- Require MFA beyond SMS. Prefer authenticator app number matching, Windows Hello for Business, or FIDO2/USB security keys for partners and administrators.
- Block legacy/basic authentication and create a Conditional Access policy that denies sign-ins without MFA from any device.
6) Reduce privilege quickly
- Remove local admin rights from standard users. Adopt Just-In-Time admin elevation for IT and use Microsoft LAPS to rotate local admin passwords automatically.
- Segment sensitive data shares and restrict “Everyone” or “Domain Users” from broad access. Map least-privilege access by practice area or client matter.
7) Turn on proven Windows security features
- BitLocker with TPM 2.0 and Secure Boot on every laptop and desktop; escrow recovery keys securely.
- Credential Guard and SmartScreen to block credential theft and malicious downloads.
- Microsoft Defender Attack Surface Reduction (ASR) rules: block Office from creating child processes; block executable content from email/web; block credential stealing.
- Controlled Folder Access to protect document libraries from ransomware encryption attempts.
8) Standardize remote access
- Disable exposed RDP from the open internet. If remote desktop is required, place it behind a VPN or a zero-trust access gateway with MFA.
- Restrict PowerShell to admins; log script block activity for auditability.

Security that respects law-firm realities is about frictionless defaults: automatic patching, MFA that partners will actually use, and backups that cannot be altered by malware. If it’s not automatic, it’s not protection—it’s a to-do item waiting to be missed.
Your 7‑day sprint: shrink attack surface and persistence paths
With the urgent gaps closed, spend the rest of the week reducing the ways attackers establish and maintain footholds.
9) Lock down email and document ingress
- Block or quarantine executables and script files arriving via email. Convert inbound Office attachments to Protected View by default.
- Enable Safe Links/Safe Attachments equivalents in your email security stack and disallow auto-forwarding outside the firm.
10) Standardize software and remove risky tools
- Create an allowlist of approved apps. Uninstall unused PDF editors, archive utilities, and legacy viewers that often carry vulnerabilities.
- Disable or restrict LOLBins (living-off-the-land binaries) where feasible, and log usage of tools like PsExec, WMI, and rundll32.
11) Implement device control
- Restrict USB storage except for approved, encrypted drives. Audit any mass storage events.
- Block unsigned drivers and enforce code integrity where supported.
12) Align to legal and client obligations
- Document controls that demonstrate reasonable efforts to protect confidentiality (e.g., encryption, MFA, patch cadence, and incident response). This supports ethical duties and client security questionnaires.
- Map controls to client requirements in engagement letters or outside counsel guidelines to reduce friction during audits.
Which controls do what? Quick comparison table
Use this table to understand the impact and business trade-offs of key Windows security controls for small legal practices.
| Control | Primary Risk Reduced | Built‑in Option | Effort | User Impact | Time to Value |
|---|---|---|---|---|---|
| Rapid Patching (Ring‑Based) | Exploitability of known vulnerabilities | Windows Update for Business / Intune / WSUS | Low–Medium | Short, planned reboots | Same day |
| Phishing‑Resistant MFA | Account takeover | Authenticator app, Windows Hello for Business, FIDO2 keys | Low | Minimal after rollout | 1–3 days |
| ASR Rules + SmartScreen | Malicious documents and scripts | Microsoft Defender for Business/Endpoint | Medium | May block rare legacy workflows | 1–2 days |
| BitLocker + Secure Boot | Data loss from device theft | Windows Pro/Enterprise native | Low | Transparent to users | Same day |
| LAPS + Least Privilege | Lateral movement via shared admin creds | Microsoft LAPS | Medium | Admins adapt workflows | 2–4 days |
| EDR with Tamper Protection | Early detection and response | Defender for Business/Endpoint | Low–Medium | Light prompts during quarantine | 1–2 days |
| Immutable 3‑2‑1‑1‑0 Backups | Ransomware impact and recovery time | NAS + object storage with immutability | Medium | None | 2–5 days |
Backups, recovery, and a 90‑minute incident drill
Backups are your last line of defense against the worst‑case scenario. If new Windows exploits lead to ransomware or destructive wipers, your ability to restore quickly determines downtime, reputational risk, and ethics reporting obligations. Make the following your standard:
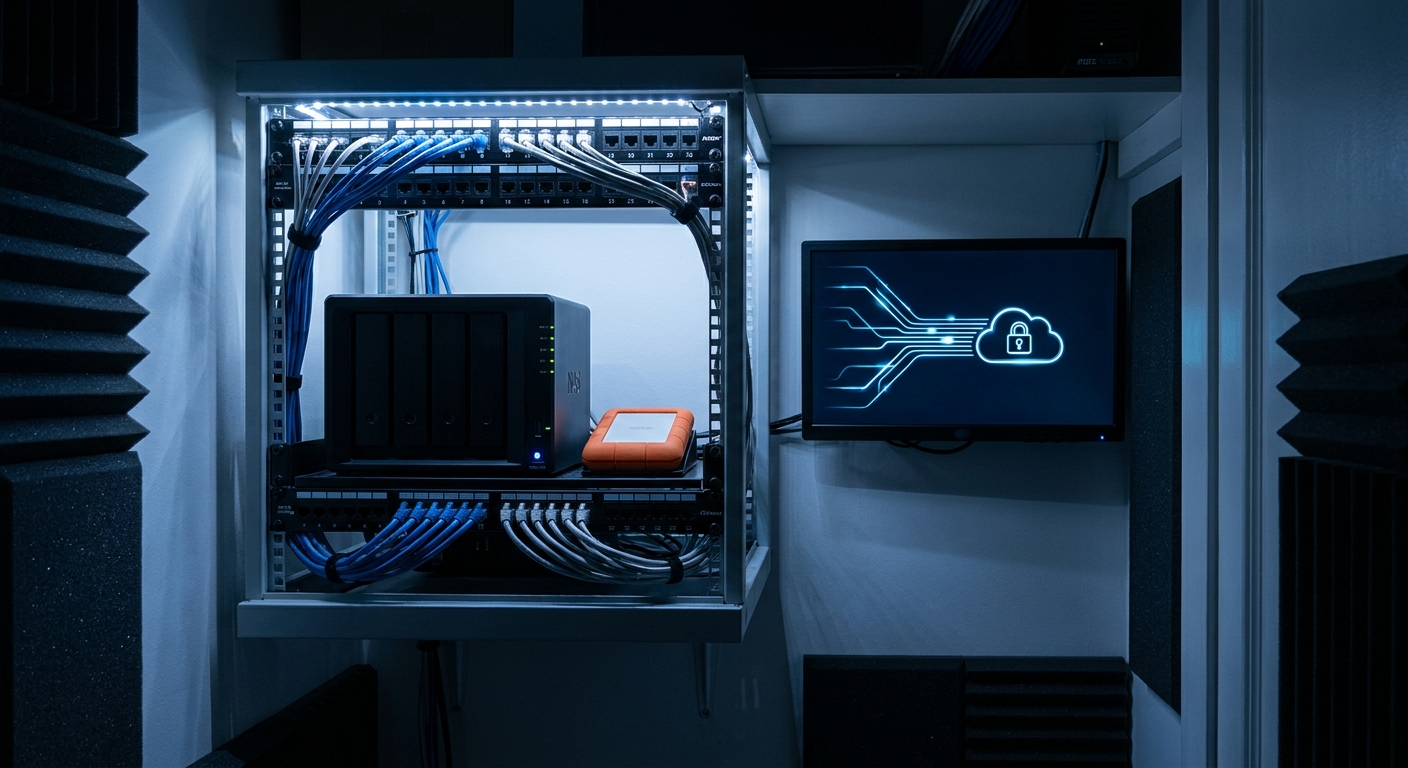
Adopt the 3‑2‑1‑1‑0 model
- 3 copies of data, on 2 different media types, with 1 offsite, 1 copy immutable/air‑gapped, and 0 unresolved restore errors after testing.
- Use a NAS or backup appliance plus cloud object storage with immutability (write‑once‑read‑many). Enable MFA and role separation for backup admin accounts.
Run a 90‑minute “tabletop + restore” drill
- Pick a core system (file share or document management system).
- Simulate a ransomware event: encrypted share, affected partner laptop.
- Start a restore from last clean snapshot; time each step to a usable state.
- Document gaps: missing credentials, slow egress, insufficient runbooks. Fix within one week.
Instrument for faster recovery
- Store encryption keys and recovery keys in a secure vault with emergency access procedures.
- Log and alert on deletion or modification of backups and snapshots; restrict who can change retention settings.
Build your small‑firm Windows security playbook
Security that survives busy season needs muscle memory. Create a short, living playbook your team actually uses.
Roles and responsibilities (RACI‑style)
- Responsible: IT lead/MSP for patching, EDR, and backups.
- Accountable: Managing partner/COO for policy approvals and client communications.
- Consulted: Practice group leads for workflow exceptions (e.g., macros, legacy apps).
- Informed: All staff via concise alerts and five-minute microtrainings.
Patch Tuesday + emergency cadence
- Monthly: ring-based updates within seven days for most devices; within 48 hours for admins and finance.
- Emergency: enable “asap” rings for high-severity exploitation in the wild; pilot on IT first, then accelerate to all staff with after-hours reboot windows.
Exception handling
- Document any ASR, macro, or driver exceptions. Set review dates every quarter. Require a business owner for each exception.
- For line-of-business apps that block updates, insist on vendor SLAs for security patches or plan an exit.
Communications templates
- Internal alert: “Security Update Tonight, 7–9 pm. Save work before 6:45 pm. Expect a reboot.”
- Client notice (if needed): “We applied critical security updates to ensure ongoing confidentiality. No client systems were impacted.”
Budget‑smart priorities for boutiques and solos
You don’t need a seven‑figure security budget to survive waves of Windows exploits. Focus spending where it materially shifts risk and improves evidence of diligence for ethics and client reviews.
Priority 1: Identity and patching (week one)
- Enforce phishing-resistant MFA; disable legacy auth.
- Turn on ring-based automated patching and reboot discipline.
Priority 2: Endpoint and data protection (month one)
- Deploy Defender for Business or a comparable EDR, enable ASR rules, BitLocker, and Controlled Folder Access.
- Standardize approved software and remove risky tools; restrict USB.
Priority 3: Recovery and monitoring (quarter one)
- Implement 3‑2‑1‑1‑0 backups with immutability and quarterly restore drills.
- Centralize logs for sign-ins, admin changes, and backup events. Review weekly.
What about servers?
- If you still run on-prem Windows servers, patch and reboot them on a strict schedule, disable SMBv1, enforce SMB signing, and limit RDP to VPN only.
- For Domain Controllers, enable read-only admin, monitor for new privileged groups, and back up system state separately.
Conclusion: move fast, then standardize
Windows exploits evolve constantly, but your defense doesn’t need to. Start with the first 24 hours—patch, verify, and raise default defenses—then lock in 72‑hour identity protections and a 7‑day attack-surface sprint. For small firms and solo practices, the winning strategy is repeatable discipline: automatic updates, phishing-resistant MFA, least privilege, EDR with tamper protection, and immutable backups you’ve actually restored. Do this and you’ll turn “breaking exploit news” into routine maintenance while preserving the client trust your practice is built on.
Ready to explore how you can streamline your processes? Reach out to A.I. Solutions today for expert guidance and tailored strategies.